Top AI-Powered Tools for Infrastructure Management in 2026

Introduction
Your platform team is drowning. Developers are shipping code faster than ever. GitHub Copilot, Cursor, and Claude are making every engineer 30–40% more productive. But the infrastructure that has to support all that code? Still largely manual. Still ticket-driven. Still requiring a platform engineer to hand-hold every IAM role change, every Terraform state migration, every compliance audit.
The gap is real: 76% of developers report cognitive overload from infrastructure complexity, even as AI makes their coding work frictionless. The bottleneck has shifted from writing code to deploying and managing the infrastructure underneath it.
In 2026, AI-powered infrastructure management tools are closing that gap fast. This post breaks down the top platforms, what they actually do, who they're built for, and where each one shines.
What Makes an Infrastructure Tool Truly "AI-Powered" in 2026?
Not every tool with "AI" in its marketing is actually AI-powered where it counts. The real distinction in 2026 comes down to three things:
Autonomous action vs. assisted action. Most tools still surface insights for humans to act on. The leading platforms in 2026 take action remediating drift, right-sizing resources, and resolving incidents without a human in the loop.
Intent-based interfaces. The best tools let engineers express what they want in natural language or high-level policy, not low-level HCL or YAML. The AI figures out how.
Continuous enforcement, not point-in-time checks. Compliance and security scans that run nightly are already outdated. The tools worth evaluating run continuously, catching drift and violations in real time.
With that baseline set, here are the tools platform engineers and SREs are actually using in 2026.
i. StackGen — Autonomous Operations Platform
What it is: An AI-native platform that uses autonomous agents to manage the full infrastructure lifecycle — from intent-based provisioning to incident remediation and continuous compliance enforcement — without requiring manual IaC authoring or human-in-the-loop toil.
Best for: Platform engineering teams that need to eliminate infrastructure toil at scale
If you've watched your platform team become a ticket queue instead of an engineering force multiplier, StackGen's Autonomous Operations Platform was built specifically for that problem.
StackGen operates through AI agents — what the team calls Aiden that work across the full infrastructure lifecycle: provisioning, governance, incident remediation, and cost optimization. Unlike tools that surface recommendations, agents act. They generate infrastructure code from high-level intent, deploy through self-validating pipelines, enforce compliance continuously, and resolve incidents autonomously, often before your on-call engineer sees the alert. What sets StackGen apart:
What sets StackGen apart:
The Intent-to-Infrastructure model is the core differentiator. Developers express what they want — "I need a Postgres cluster in us-east-1 with read replicas and automated backups" and Aiden generates the Terraform, validates it against your policy guardrails, and deploys it. No ticket. No three-day wait. No state file conflict because a platform engineer was hand-editing HCL.
For compliance teams, this is a game-changer. Every change is logged, policy-enforced, and auditable. Teams running SOC 2, HIPAA, or FedRAMP audits report dramatically reduced time in the infrastructure section because the drift between what's in code and what's actually deployed is caught and corrected continuously, not discovered during an audit.
| 95% Less IaC effort for developers |
10x Less manual work for platform teams |
35% Fewer compliance issues |
5–15 min MTTR (down from 2–4 hrs) |
|---|
Autonomy you control. Aiden agents operate within the guardrails that your team defines. Most teams start in recommend-and-approve mode for sensitive changes (production deployments, IAM policy updates) and expand autonomy as confidence builds. Every decision is logged — which matters when your auditor asks who approved a change six months ago.
StackGen works on top of your existing toolchain — Terraform, Pulumi, Helm, ArgoCD, Prometheus, and Grafana. It doesn't replace your stack; it drives it.
MCP Server: Infrastructure From Your IDE
The StackGen MCP Server extends Aiden's capabilities directly into the developer's IDE. Your team is already using Claude, Cursor, and GitHub Copilot to write code faster — but every time they need infrastructure, they're back to filing tickets and switching contexts.
With the StackGen MCP Server, that context switch disappears. Developers type natural language prompts directly in Claude or Cursor — "Deploy my Python app to AWS ECS" or "Check if my production stack has any drift" — and StackGen's infrastructure agents execute against your actual cloud environment, with all your governance guardrails intact.
The MCP server provides 25+ tools covering the complete infrastructure lifecycle from within your IDE:
- Provision multi-cloud infrastructure — Deploy AppStacks across AWS, Azure, and GCP from a single conversational prompt
- Import existing resources — Use Cloud2Code to convert running cloud resources into managed IaC without starting from scratch
- Detect and remediate drift — Identify configuration gaps between deployed and desired state, then fix in one command
- Enforce governance inline — Security policies, compliance rules, and IAM restrictions apply automatically — Claude and Cursor don't bypass your guardrails
Explore the StackGen Platform → | See Aiden for Platform Engineering →
ii. Terraform Cloud / HCP Terraform (HashiCorp)
 What it is: A managed platform that adds remote state storage, team collaboration workflows, policy enforcement via Sentinel, and AI-assisted module generation on top of the industry-standard Terraform IaC language.
What it is: A managed platform that adds remote state storage, team collaboration workflows, policy enforcement via Sentinel, and AI-assisted module generation on top of the industry-standard Terraform IaC language.
Best for: Teams already deep in the HashiCorp ecosystem who want managed state and collaboration
Terraform remains the dominant IaC language, and HCP Terraform (the renamed Terraform Cloud) adds the managed infrastructure around it: remote state storage, concurrent plan/apply runs, policy-as-code with Sentinel, and a collaborative workflow for team-based infrastructure changes.
In 2026, HashiCorp added AI-assisted module generation that can suggest Terraform configurations from natural language inputs. It's a meaningful improvement for teams who want to stay within the HashiCorp ecosystem.
Where it shines: The module registry, existing integrations, and the sheer breadth of provider coverage. If your team is already fluent in HCL, the learning curve is minimal.
Where it falls short: The licensing changes that started with BSL in 2023 continue to sting for teams with large workload counts. Per-workspace pricing at scale can become significant. And HCP Terraform is still fundamentally a collaboration layer around Terraform; it doesn't autonomously remediate drift, respond to incidents, or generate infrastructure from intent the way purpose-built AI platforms do.
If you're evaluating HCP Terraform and feeling the pricing pressure, StackGen's DevOps Infrastructure solution is a direct migration path that adds AI-native automation on top of your existing Terraform codebase.
iii. Pulumi — Infrastructure as Code with Real Languages
 What it is: An IaC platform that lets teams write infrastructure code in Python, TypeScript, Go, or C# instead of domain-specific languages, paired with an AI copilot that generates Pulumi programs from natural language and helps debug provider errors inline.
What it is: An IaC platform that lets teams write infrastructure code in Python, TypeScript, Go, or C# instead of domain-specific languages, paired with an AI copilot that generates Pulumi programs from natural language and helps debug provider errors inline.
Best for: Engineering teams who want IaC in Python, TypeScript, Go, or C# instead of HCL
Pulumi's value proposition is simple: your engineers already know Python. Why learn another domain-specific language for infrastructure? Pulumi lets teams write infrastructure code in real programming languages, complete with loops, conditionals, testing frameworks, and IDE support.
In 2026, Pulumi AI has gotten meaningfully better at generating Pulumi programs from natural language prompts. The Pulumi Copilot can suggest resource configurations, explain stack outputs, and help debug provider errors.
Where it shines: Developer experience for teams that find HCL limiting. The ability to unit test infrastructure code and import existing cloud resources into Pulumi state is genuinely useful.
Where it falls short: Pulumi Copilot is still in the "assisted" category it helps you write IaC faster, but it doesn't autonomously provision, govern, or remediate. You still need engineers doing the hands-on work. For teams where the bottleneck is toil (not just authoring speed), adding an AI writing assistant to a manual process doesn't move the needle enough.
iv. Ansible Automation Platform (Red Hat)
 What it is: An enterprise-grade automation platform built on Ansible's agentless YAML playbook model, extended with execution environments, event-driven triggers, and Ansible Lightspeed — an AI assistant that generates playbooks from natural language task descriptions.
What it is: An enterprise-grade automation platform built on Ansible's agentless YAML playbook model, extended with execution environments, event-driven triggers, and Ansible Lightspeed — an AI assistant that generates playbooks from natural language task descriptions.
Best for: Configuration management, application deployment, and hybrid cloud orchestration
Ansible's declarative YAML playbooks have been the backbone of configuration management for over a decade. Red Hat's Ansible Automation Platform adds enterprise features: execution environments, automation controller, private automation hubs, and the Event-Driven Ansible capability that triggers playbooks based on real-time events.
The 2026 addition of Ansible Lightspeed (AI assistant) generates playbooks from natural language task descriptions, which meaningfully lowers the barrier for teams building new automation.
Where it shines: Breadth of integrations. Ansible modules exist for virtually every cloud resource, network device, and enterprise application. For hybrid environments mixing on-premises and cloud, Ansible's agentless architecture is a real advantage.
Where it falls short: Ansible is a task executor, not an autonomous operations platform. It does what you tell it to do. For platform teams dealing with constant drift, compliance gaps, and incident response, Ansible still requires someone to define, trigger, and monitor every playbook. The operational overhead of maintaining a large Ansible playbook library is itself a form of toil.
v. Brainboard — Visual AI-Driven Infrastructure Design
 Best for: Platform engineering teams building internal developer platforms on Kubernetes
Best for: Platform engineering teams building internal developer platforms on Kubernetes
What it is: An AI-powered platform that lets teams visually design cloud infrastructure through a drag-and-drop interface and automatically generates production-ready Terraform code from those designs — combining visual collaboration, AI code generation, drift detection, and an embedded CI/CD pipeline in a single tool.
Brainboard bridges the gap between how engineers think about infrastructure (architecturally, visually) and how they define it (declarative code). Draw your cloud topology — VPCs, subnets, load balancers, databases — and Brainboard's AI layer generates the corresponding Terraform code automatically, keeping diagram and code in sync.
Where it shines: Visual-first design makes IaC accessible to engineers who aren't Terraform experts. Particularly strong for onboarding and documentation. Drift detection flags when deployed infrastructure diverges from the designed state, and the embedded CI/CD pipeline means no separate orchestration layer is needed for deployment. RBAC and secure remote backend management round out the enterprise features.
Where it falls short: Brainboard is fundamentally a design and code generation tool — the AI generates IaC, but humans still review and apply it. No autonomous remediation, no incident response, no real-time policy enforcement loop. Most valuable for teams in the IaC authoring and standardization phase.
vi. Spacelift — IaC Orchestration and Policy Enforcement
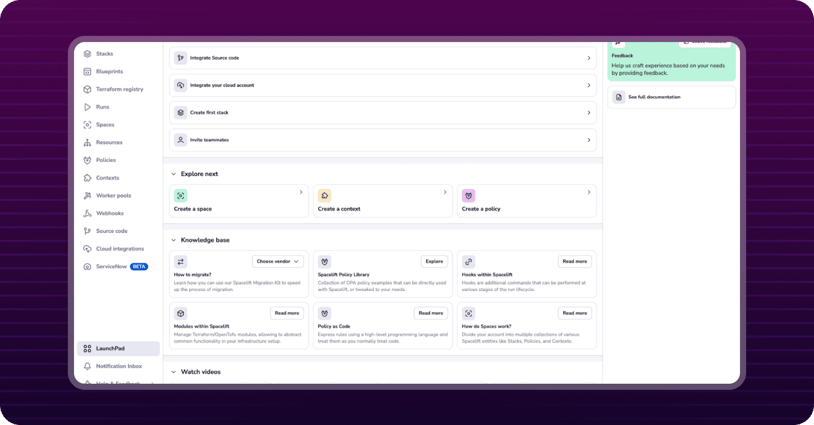
What it is: A CI/CD and workflow orchestration layer for infrastructure-as-code that manages stack dependencies, drift detection, and OPA-based policy enforcement across Terraform, OpenTofu, Pulumi, and Kubernetes configurations.
Best for: Multi-cloud teams that need a workflow orchestration layer over Terraform, OpenTofu, and Pulumi
Spacelift positions itself as the CI/CD layer for infrastructure — managing stacks, handling dependencies between them, enforcing policies with OPA, and providing a pull-request-based workflow for infrastructure changes.
Where it shines: If you're running Terraform at scale with complex stack dependencies, Spacelift's drift detection and stack dependency graphs are genuinely useful. The OPA integration for policy-as-code is more flexible than Sentinel for teams with complex governance requirements.
Where it falls short: Spacelift is still a workflow orchestration tool — it makes your existing IaC process better, but it doesn't fundamentally automate it. Drift gets detected and surfaced; engineers still remediate. That's a meaningful gap from what purpose-built AI platforms deliver.
vii. env0 — Cost-Controlled IaC Management
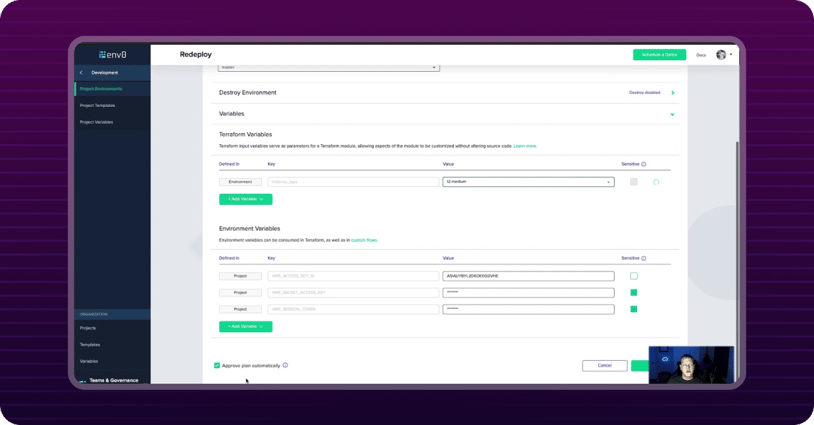
What it is: An IaC workflow management platform with built-in FinOps controls — TTL-based environment expiration, per-environment cost tracking, budget-gated approval workflows, and self-service provisioning — designed specifically to prevent cloud waste from ephemeral dev and staging environments.
Best for: FinOps teams that need visibility and controls around infrastructure spend
env0 combines IaC workflow management with built-in cost controls: TTL-based environment expiration, budget alerts, approval workflows gated on cost thresholds, and per-environment cost tracking.
Where it shines: If runaway cloud spend from ephemeral dev environments is a real problem for your team, env0's cost controls are purpose-built for that scenario. The self-service environment provisioning model is well-designed.
Where it falls short: env0 is focused on the pre-deployment workflow and cost visibility layer. It doesn't address the operational side of incident response, compliance enforcement, or ongoing infrastructure governance.
The Compliance Trigger Teams Keep Underestimating
Here's a pattern we see consistently: teams evaluate AI infrastructure tools based on developer velocity and toil reduction, and those are real pain points. But the buying decision often gets made faster because of compliance.
When your security team mandates policy-as-code and gives you 60 days, or when you fail an audit because you can't prove who approved an infrastructure change six months ago, the urgency is acute. Drift between what's in code and what's actually deployed is a compliance time bomb, and it's one that fires on a schedule you don't control (your auditor's).
Tools that offer continuous drift detection and automated remediation with full audit trails don't just reduce toil. They make the infrastructure section of your next SOC 2 audit something your team can walk through without breaking a sweat.
StackGen's Autonomous Operations Platform was designed for exactly this: every change logged, every deviation from the desired state caught and corrected in real time, every approval workflow auditable.
Frequently Asked Questions
Q: Can AI infrastructure tools work alongside our existing Terraform codebase?
Yes — the leading platforms are designed to work with, not replace, your existing toolchain. StackGen, for example, operates on top of Terraform, Pulumi, Helm, and ArgoCD. The AI layer drives the automation; your existing code remains the source of truth.
Q: How do teams typically pilot AI infrastructure automation?
Most teams start with a single high-toil workflow — often infrastructure drift remediation, alert noise reduction, or automated incident response for known failure patterns. A typical pilot runs 4–6 weeks on non-production environments, with measurable toil reduction visible within the first two weeks.
Q: What does "autonomous" actually mean — do agents take action without human approval?
You control the autonomy level. Platforms like StackGen let you configure guardrails per workflow — fully autonomous for well-understood operations (right-sizing non-production resources, remediating known drift) and human-in-the-loop approval for sensitive changes (production deployments, IAM policy updates). Most teams start conservatively and expand autonomy as trust builds.
Q: How do AI tools handle compliance audit requirements?
Purpose-built platforms log every action and decision with full attribution — who (or which agent) made a change, what the policy justification was, and what the before/after state was. This makes audit preparation dramatically faster than reconstructing a change history from git blame and Slack archaeology.
Conclusion
The infrastructure management landscape in 2026 has a clear fault line: tools that assist engineers in doing the same manual work faster, and platforms that change what engineers need to do in the first place.
For platform teams where the bottleneck is toil — Terraform state conflicts, IAM ticket queues, 2 AM alert pages, compliance archaeology — tools in the "assisted" category won't move the needle enough. The teams closing that gap are deploying AI agents that take action autonomously, operate within defined guardrails, and treat infrastructure operations as a continuously solved problem rather than a continuously repeated one.
StackGen's Aiden for Infrastructure and Autonomous Operations Platform are built for exactly that transition.
Ready to see what autonomous infrastructure operations look like for your team?
About StackGen:
StackGen is the pioneer in Autonomous Infrastructure Platform (AIP) technology, helping enterprises transition from manual Infrastructure-as-Code (IaC) management to fully autonomous operations. Founded by infrastructure automation experts and headquartered in the San Francisco Bay Area, StackGen serves leading companies across technology, financial services, manufacturing, and entertainment industries.
